A strange kind of web traffic is spreading across dashboards, and it’s showing up right as deepfake scams are getting frighteningly good. Together, these two trends are pushing crypto security teams, publishers, and enterprises into the same uncomfortable reality: the signals we rely on are becoming easier to fake and harder to trust.
Ghost traffic is polluting the internet’s “truth”
Over the past several months, many small sites, companies, and even government teams have noticed something unusual in their analytics. Sessions appear to surge from places like Lanzhou and Singapore, but the visits don’t behave like real users. They often don’t reach servers in a normal way, don’t trigger typical firewall activity, and don’t leave the usual technical footprints.
What makes this more damaging than simple spam is how believable it looks inside GA4. These bots can trigger measurement events and copy basic browsing patterns well enough to inflate sessions, engagement, and campaign reports. For smaller publishers especially, a few hundred fake visits can completely change performance trends, ad results, and marketing decisions.
Deepfakes are now good enough to beat instinct
At the same time, identity fraud has entered a new phase. Deepfake audio and video are improving so fast that “trust your gut” is no longer reliable.
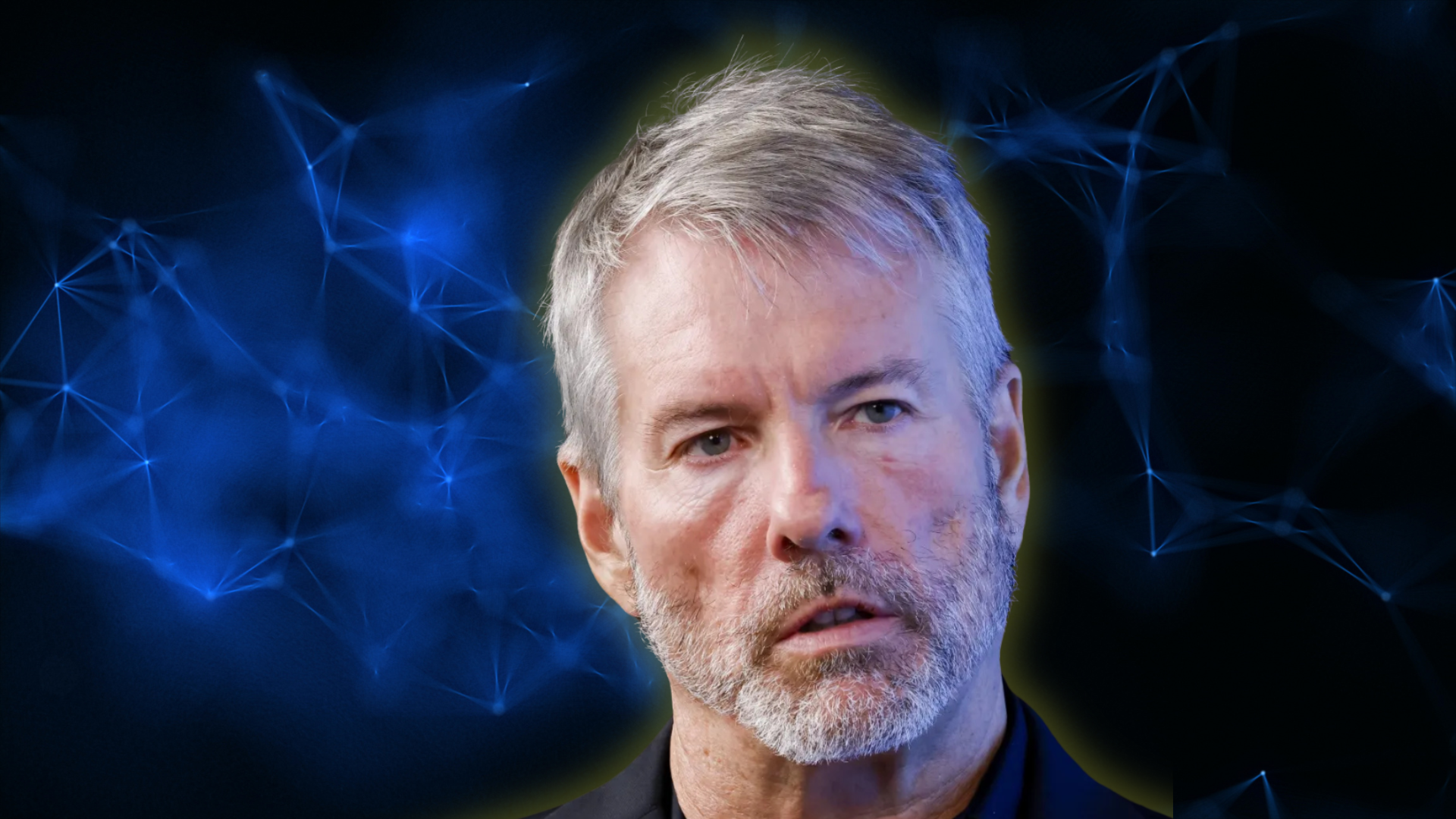
Changpeng Zhao (CZ) recently warned that an AI-generated voice clip in Mandarin was so accurate he couldn’t confidently tell it apart from his real voice. His point is simple and scary: if a voice can be cloned perfectly, then even video-call verification won’t be a strong security checkpoint for much longer.
That warning comes alongside real-world incidents where AI-generated “people” joined meetings convincingly enough to persuade teams to move large sums of money, turning standard corporate processes into high-value targets.
CZ’s privacy paradox: transparency helps attackers
CZ is also linking these threats to a deeper issue in both the internet and public blockchains: extreme transparency can become a weapon.
He argues that privacy is a basic right, but today’s public chains reveal too much once identities are linked to addresses. If a company pays salaries on-chain, it can expose who earns what. Vendor relationships, operational spending, and payment patterns can become visible. Once you add KYC connections, it becomes even easier to map real people to wallets and trace behavior.
In other words, transparency can be good for auditability, but it can also create a rich data layer for attackers, scrapers, and brokers—especially when AI tools can analyze patterns at scale.
Why bot traffic and deepfakes are part of the same crisis
On the surface, fake website sessions and face-swapped executives look like separate problems. In reality, they share the same effect: they break digital trust.
If analytics can be manipulated without real visitors, then business decisions can be pushed in the wrong direction. If video calls can be forged, then identity checks become less meaningful. When both happen at once, it becomes harder to answer basic questions like “Who is this?” and “Did this really happen?”
This is where crypto intersects with the broader security debate. The industry is built around verification, yet it still depends on signals (identity, intent, traffic, communications) that AI can now imitate.
The path forward: verify integrity without exposing everything
CZ isn’t calling for blockchains to hide everything. He’s pushing for systems that can prove what matters—without leaking sensitive details.
That points to privacy-preserving tools such as zero-knowledge proofs, plus stronger identity rails that can confirm a person is real and authorized, while limiting what gets revealed about finances and internal workflows. The goal is a world where authenticity and consent can be checked cryptographically, but personal and corporate data isn’t left open by default.
What this means for crypto security right now
For teams building in crypto, the lesson is getting clearer:
- Security isn’t only about protecting funds anymore. It’s also about protecting signals.
- Bots can distort growth metrics and ad value. Deepfakes can bypass human verification.
- Public-chain transparency can expose operational data that attackers can exploit.
- Privacy and transparency must work together: prove integrity, protect sensitive details.
In an AI-saturated environment, “looks real” is no longer a reliable standard. The next era of crypto adoption especially for payments will depend on whether the industry can make verification stronger while keeping people and businesses safe from unwanted exposure.