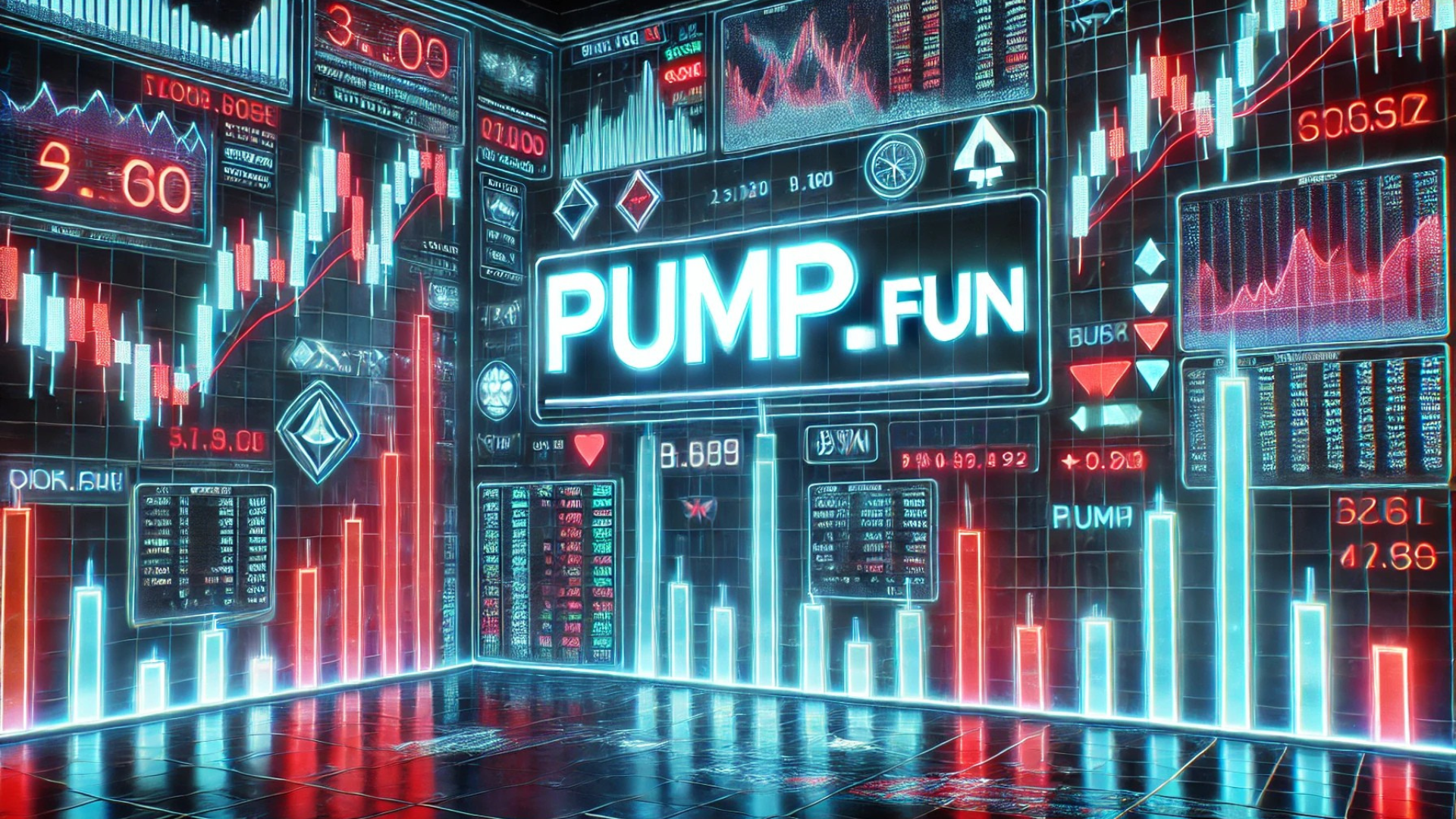
A new type of malware called JSCEAL is making waves in the cyber security world due to its ability to disguise itself as major cryptocurrency platforms to steal valuable crypto-related data. According to Check Point Research, the malware has been active since March 2024 and is becoming increasingly sophisticated. Here’s a breakdown of how JSCEAL works and how it’s targeting crypto users.
How JSCEAL Works
JSCEAL operates by impersonating popular crypto platforms such as Binance, MetaMask, eToro, Kraken, and Monero, among others. The malware lures victims through ads that lead them to fake websites, often making them believe they’re downloading legitimate apps for trading crypto. However, these apps are actually malicious, designed to infiltrate users’ devices and steal sensitive crypto-related information.
The malware is difficult to detect, thanks to its “unique anti-evasion methods.” It uses a combination of JavaScript, compiled code, and heavy obfuscation to make detection harder. JSCEAL doesn’t require the user to interact with the code for it to execute, which adds to its stealthiness. Once installed, the malware steals a wide range of data, including passwords, network details, email information, and even autocomplete passwords. It also tracks the victim’s location and collects proxy configurations.
In some cases, the attackers even add additional layers to the malware that can download more harmful code, potentially erasing all traces of the malware from the system to cover their tracks.
The Scale of the Attack
According to Check Point, in the first half of 2025, the malware campaign reached around 35,000 malicious ads, leading to millions of views in the European Union alone. The security firm estimates that each ad potentially reached at least 100 users, meaning that these ads could have affected 3.5 million users in the EU. With the global reach of social media, the firm believes the total number of affected users could easily surpass 10 million worldwide.
The Impact on Crypto Users
JSCEAL’s main objective is to harvest data from infected devices and send it to the hacker’s server. The malware is able to gather crucial machine information and sensitive data like passwords and network details. While it’s still possible to use anti-malware software to detect and stop attacks, the clever methods employed by JSCEAL make it particularly tricky to combat.
The campaign continues to evolve, and it’s clear that crypto users need to remain vigilant, as this new form of attack could lead to significant losses if left unchecked.
What You Can Do to Protect Yourself
- Be cautious when downloading any software or clicking on ads related to crypto platforms.
- Ensure you’re visiting legitimate websites by double-checking URLs.
- Use robust anti-malware software and regularly update it.
- Stay informed about the latest threats in the crypto space and be cautious with the platforms you trust.
In conclusion, JSCEAL is a dangerous malware that’s specifically targeting crypto users by impersonating trusted platforms. Its sophisticated methods make it hard to detect, but awareness and proactive security measures can help protect your data from these evolving threats.