A new investigation by Mandiant has uncovered that the $1.4 billion hack on Bybit, the largest crypto theft in history, was orchestrated by North Korean hacking group TraderTraitor. The attack was initiated through a malware-laced fake stock investment project that compromised a Safe{Wallet} developer’s Mac laptop and allowed hackers to bypass Amazon Web Services (AWS) security.
How the Breach Occurred
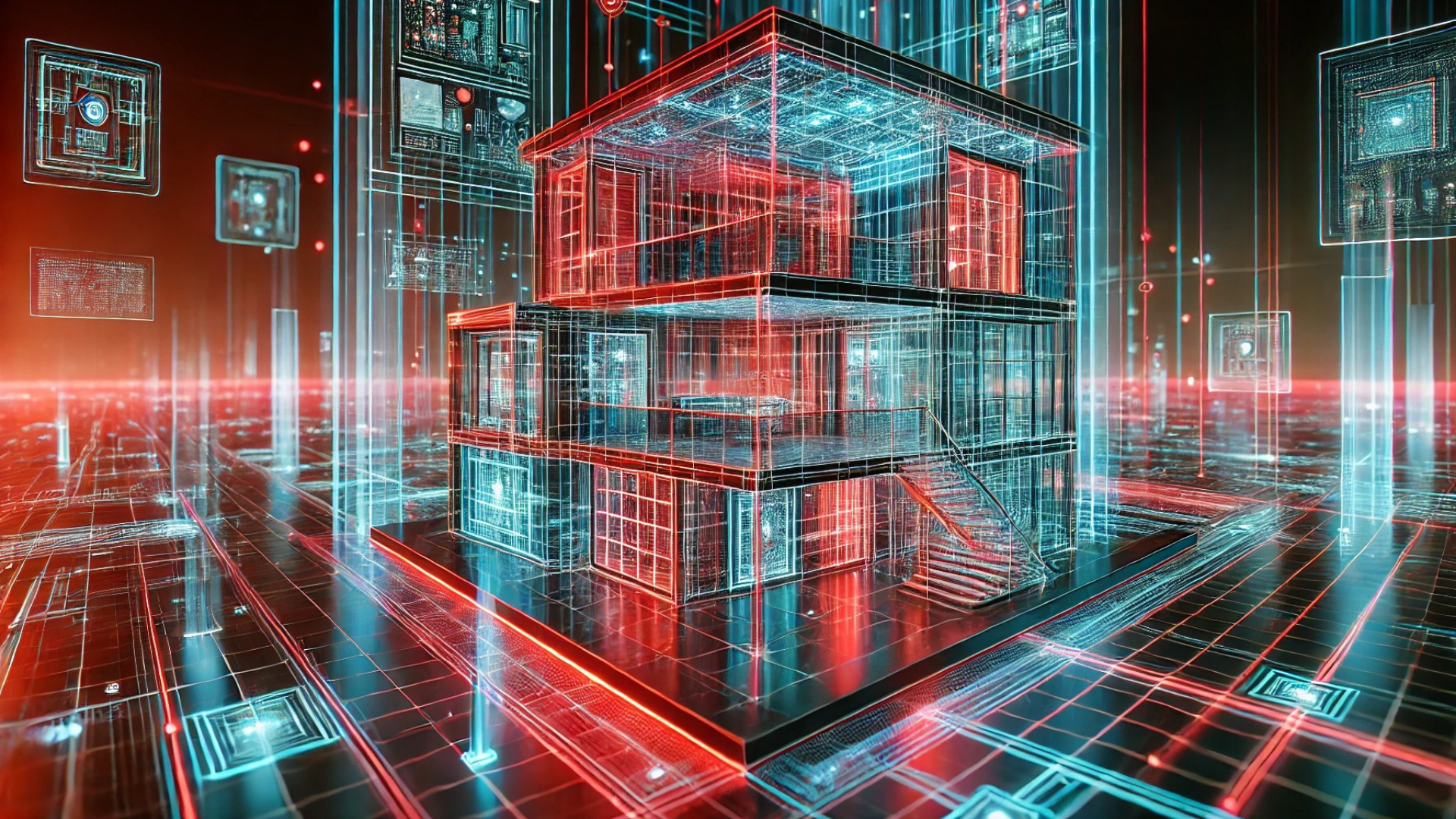
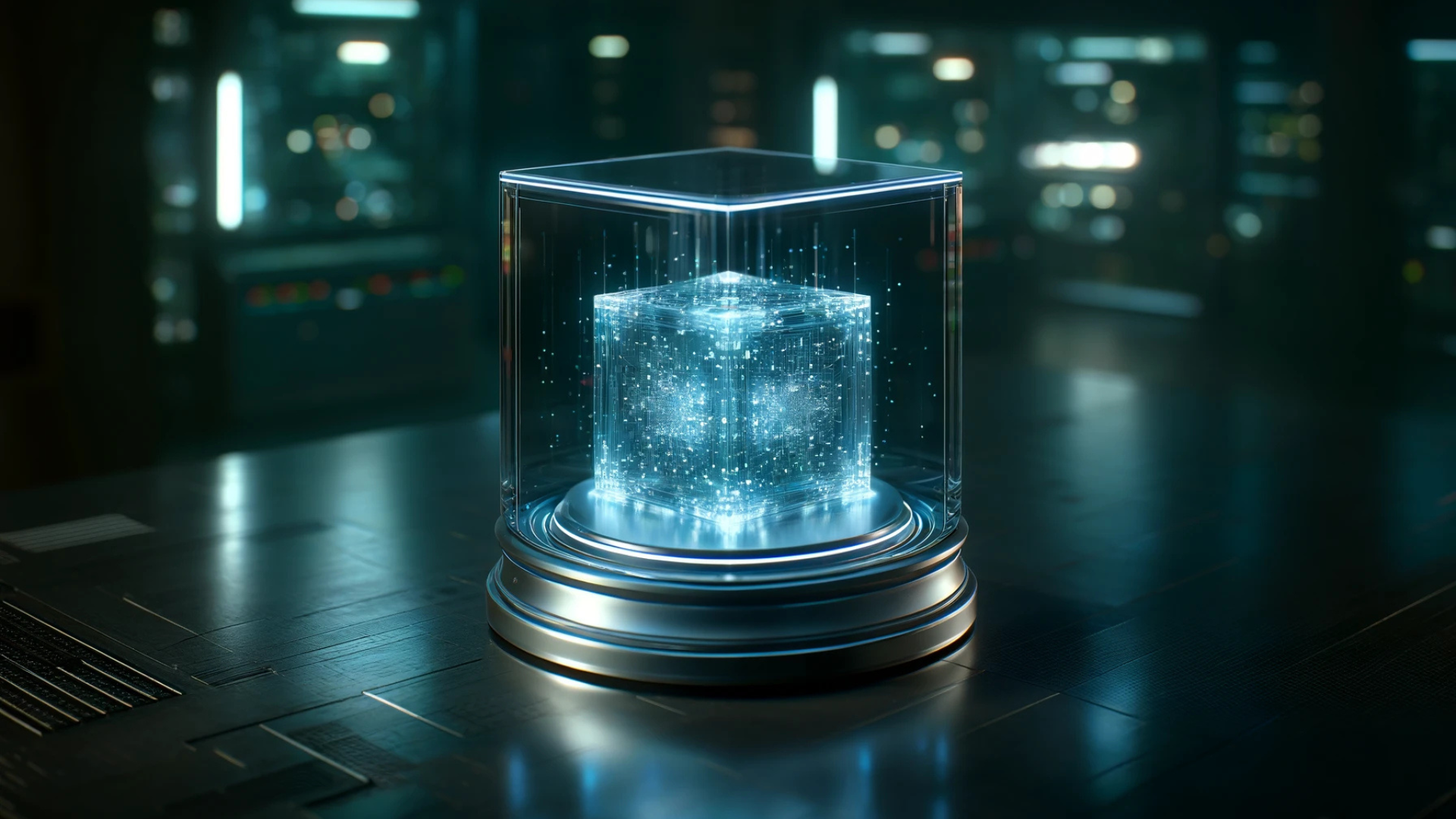
According to Mandiant’s investigation, the attack began on February 4, 2025, when a Docker project posing as a stock investment simulator was downloaded onto a Safe{Wallet} developer’s Mac, identified as “Developer1.”
This malware-laced project communicated with a suspicious domain, getstockprice[.]com, enabling the hackers to install malicious software. Once inside, TraderTraitor leveraged stolen AWS session tokens to bypass multi-factor authentication (MFA), gaining unauthorized access to critical AWS services.
“Certain gaps in fully recovering certain aspects of the attack remain because the attacker removed their malware and cleared Bash history in an effort to thwart investigative efforts.” – Safe
Bypassing AWS Security
The attackers used hijacked AWS session tokens, allowing them to authenticate without re-entering MFA credentials. These tokens provided seamless access to AWS resources, evading security measures. The attack was conducted from IP addresses linked to VPN services and offensive security tools, further obscuring their tracks.
Safe{Wallet} and Bybit’s Response
Following the breach, Safe{Wallet} implemented infrastructure resets and restricted external access to prevent further compromises. It also partnered with Blockaid, a blockchain security firm, to improve detection of malicious transactions. Notably, Safe confirmed that its smart contracts were not affected by the incident.
Meanwhile, Bybit CEO Ben Zhou disclosed in early March that approximately 20% of the stolen funds have become untraceable. While around 77% of the stolen funds remain traceable, cybercriminals have laundered nearly 20% through crypto-mixing services, making recovery significantly more challenging.
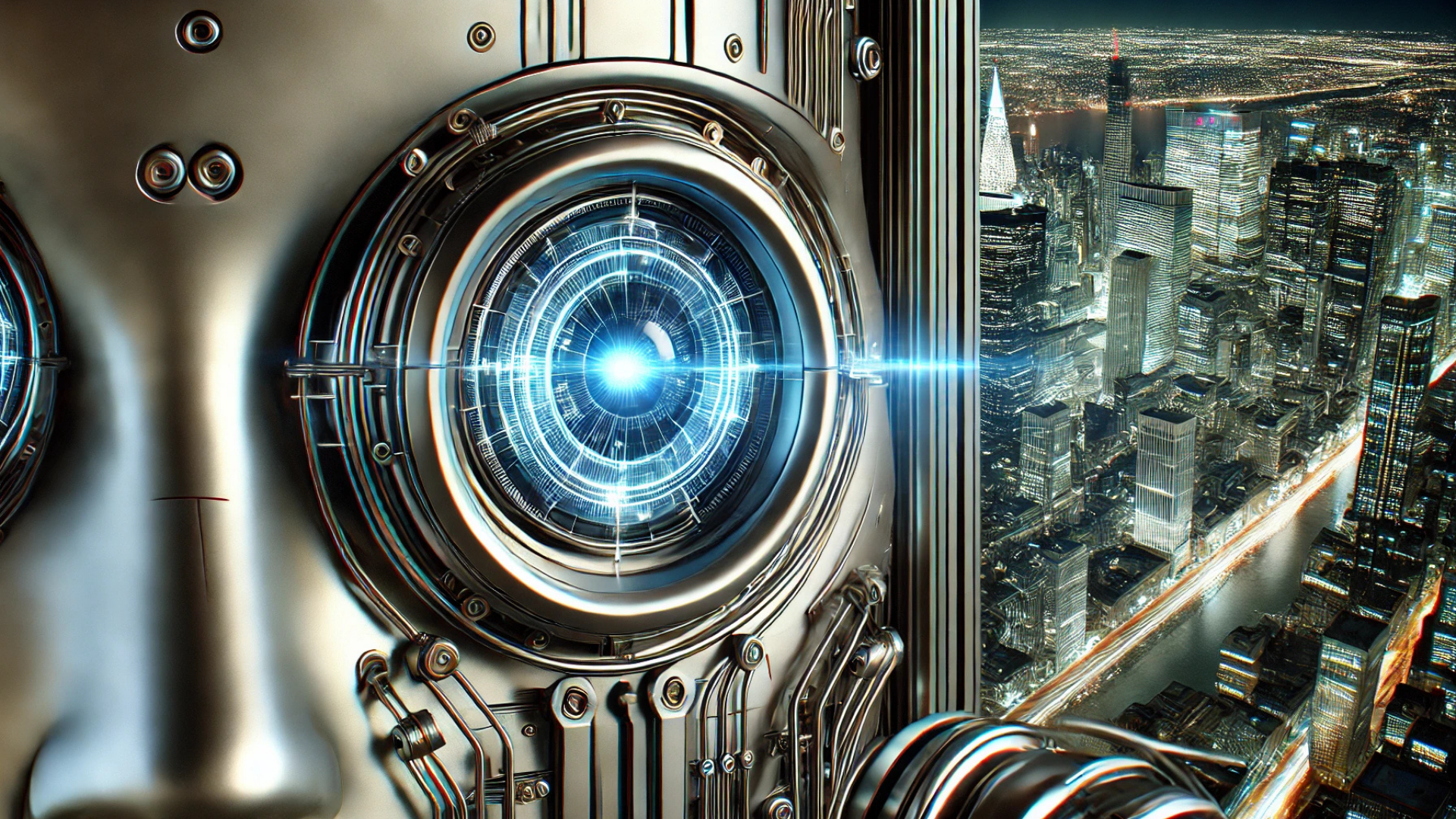
Implications of the Bybit Hack
The attack underscores the increasing sophistication of state-sponsored cybercrime, particularly from North Korean groups targeting cryptocurrency firms. It also highlights vulnerabilities in cloud-based security infrastructure, emphasizing the need for stronger endpoint security measures and enhanced multi-factor authentication protections.
Bybit continues working with blockchain forensic firms and law enforcement agencies to recover stolen funds and strengthen its security framework, while the broader crypto industry reassesses its security protocols in response to this record-breaking cyber heist.